What is Azure Bastion?
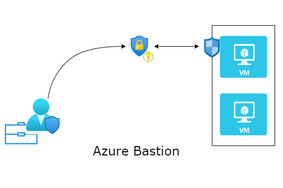
Azure Bastion is a PaaS service of Azure, allows you connect to an Azure virtual machine using your browser and provides secure and seamless RDP/SSH connectivity directly from the Azure portal over TLS. In a typical RDP connection, a virtual machine needs to configure a public IP that is exposed to the world and a client machine uses that IP and login credentials to connect and login to the virtual machine. When you connect via Azure Bastion, your virtual machines do not need a public IP address, agent, or special client software.
Bastion provides secure RDP and SSH connectivity to all of the VMs in the virtual network in which it is provisioned. Using Azure Bastion protects your virtual machines from exposing RDP/SSH ports to the outside world, while still providing secure access using RDP/SSH.
Key Benefits of Azure Bastion:
- You can get to the RDP and SSH session directly in the Azure portal using a single click seamless experience.
- Azure Bastion uses an HTML5 based web client that is automatically streamed to your local device. You get your RDP/SSH session over TLS on port 443, enabling you to traverse corporate firewalls securely.
- Azure Bastion opens the RDP/SSH connection to your Azure virtual machine using private IP on your VM. You don’t need a public IP on your virtual machine.
- Azure Bastion is a fully managed PaaS service from Azure that is hardened internally to provide you secure RDP/SSH connectivity. You don’t need to apply any NSGs to the Azure Bastion subnet. Because Azure Bastion connects to your virtual machines over private IP, you can configure your NSGs to allow RDP/SSH from Azure Bastion only.
- Because you do not need to expose your virtual machines to the public Internet, your VMs are protected against port scanning by rogue and malicious users located outside your virtual network.
- Azure Bastion is a fully platform-managed PaaS service. Because it sits at the perimeter of your virtual network, you don’t need to worry about hardening each of the virtual machines in your virtual network. The Azure platform protects against zero-day exploits by keeping the Azure Bastion hardened and always up to date for you.
RDP vs SSH vs Bastion
RDP is a Windows protocol, used to access remote Windows virtual machines and Windows servers. RDP requires a port to be opened on the remote machine, VM or physical server. Because RDP ports are often opened to the Internet and available publicly, they are often attacked by the hackers and bots. To protect RDP instances, companies often use a virtual private network and a form of multi factor authentication (MFA).
SSH (Secure Shell) protocol similar to RDP allows a client machine to communicate to another machine (server) and transfer data. The advantage of SSH is it protects the communications security and integrity with strong encryption.
SSH protocol is used in corporate networks for:
- Providing secure access for users and automated processes
- Interactive and automated file transfers
- Issuing remote commands
- Managing network infrastructure and other mission-critical system components.